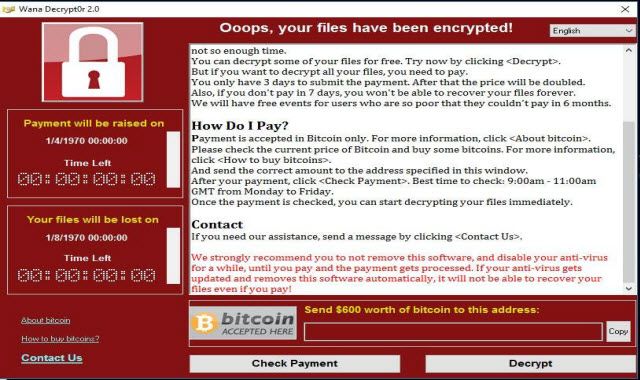
WannaCry ransomware attack
WannaCry ransomware hits almost two hundred countries like a tsunami. Encrypting hundreds of thousands computers worldwide.
Advertisements
Europe was the most affected, in fact the NHS in Britain was force to cancel surgeries and other medical services. Russia, China and other US and Asian countries were also affected. The list below are some organizations that were also victimized;
- Ministry of Internal Affairs of the Russian Federation
- Ministry of Foreign Affairs
- National Health Service (England)
- NHS Scotland
- Nissan Motor Manufacturing UK
- PetroChina
- Portugal Telecom
- Q-Park
- Renault
- Russian Railways
- Sandvik
- São Paulo Court of Justice
- Saudi Telecom Company
- Sun Yat-sen University
IS WannaCry ransomware still a threat?
Yes, it is still a big threat (as of this writing) if you are not careful. Fortunately, one of the Cyber Security expert named “Malwaretech” was able to find its so-called “kill-switch”.
Thus, slowing down the spread of Wanna Decryptor or Wannacry. Remember, it was just slowed down, not gone. Presuming it was gone, a second wave of Wannacry still possible as other expert said.
Advertisements
How to protect your computer(s) against Wannacry?
Commonsense. Yes, you read it right. Actually, it’s the best weapon better than antivirus itself. I wrote about it here 11 ways to prevent computer virus and malware : Safety First. Simple steps to protect your devices against WannaCry are as follows:
- Update or upgrade your OS (Operating System). Windows XP users are the most affected, given that Microsoft already stopped the updates 3 years ago. There were reports that Windows 10 has zero WannaCry cases. You can get the update mentioned here Microsoft Security Bulletin MS17-010 . For Windows XP users get the special update here.
- Install a paid antivirus with built-in anti-ransomware. Ransomware has become one of the most popular security threat. The reason, that most antivirus vendor already included it in their security features. Malwarebytes, SmadAV and other popular brands boast its Anti-ransomeware capability.
- Do not click links from unknown sites, on chat rooms and messengers.
- Do not open emails from unknown sender and don’t ever click its links. Ransomware usually executed through email links by way of spamming and phishing.
- Always back-up your important Data. The reason wannacry is called ransomware because like other ransomware variants it will lock your computer through encryption. Then, it will ask for a payment in exchange of a key to decrypt your data again. So, if you back up your files you will worry less. All you need is time and effort to retrieve your data.
Wannacry Ransomware infected my computer!
As of this writing Wannacry Ransomware already accumulated 220 payments that’s worth $59,747.53. Well, I must confess that paying the ransomware developer is an option to decrypt your files but it is discouraged. Because it will encourage them to create more ransomware. So, what should you do?
You need to remove the Wanna cry ransomware. Download Rkill, SmadAV and Malwarebytes.
- Run Rkill to scan and kill any Sysprotector Registry variants. Please take note that after Rkill stops the processes, do not turn off or restart your computer. Then, install and run SmadAV, remove all malicious software detected. Finally, scan your computer with malwarebytes, remove all malicious programs detected. Then follow these guide How to protect your computer(s) against Wannacry?
The steps above will just remove the wannacry infection. The files encrypted by wannacry remains encrypted. Sad to say, that there is no way to decrypt your files for free. You need to hire a professional to do it for you.
Advertisements
WAIT! There were information that Wannacry Ransomware did not encrypt the actual files. Instead it creates a copy or shadow of the actual files and encrypt it while deleting the actual files. If this is true;
- A Data recovery might be an option.
- Windows system restore is also worth trying.
- Booting your computer with Linux is also considered a way of recovering your encrypted data. Once you are in Linux environment try to open and copy your files to external storage. A forum here states that wannacry failed to infect Linux OS.
- Linux based Data recovery like parted magic may also help.
If anyone of you discovered a new way and free methods of decrypting wannacry encrypted files. You are welcome to share it here.

Advertisements